The Onion Router (TOR)
The Onion Router or Tor, for short is an open-source software which enables user's online privacy, it does so by routing the users network traffic over a world wide network called relays, relays are also known as "routers" or "nodes." When a user uses Tor the users IP address remains hidden which sounds similar to a VPN or a Proxy server but unlike a VPN or a Proxy, all the traffic is encrypted with multiple layers of encryption and is sent through random nodes before connecting the user to the destination be it a website or anything else.
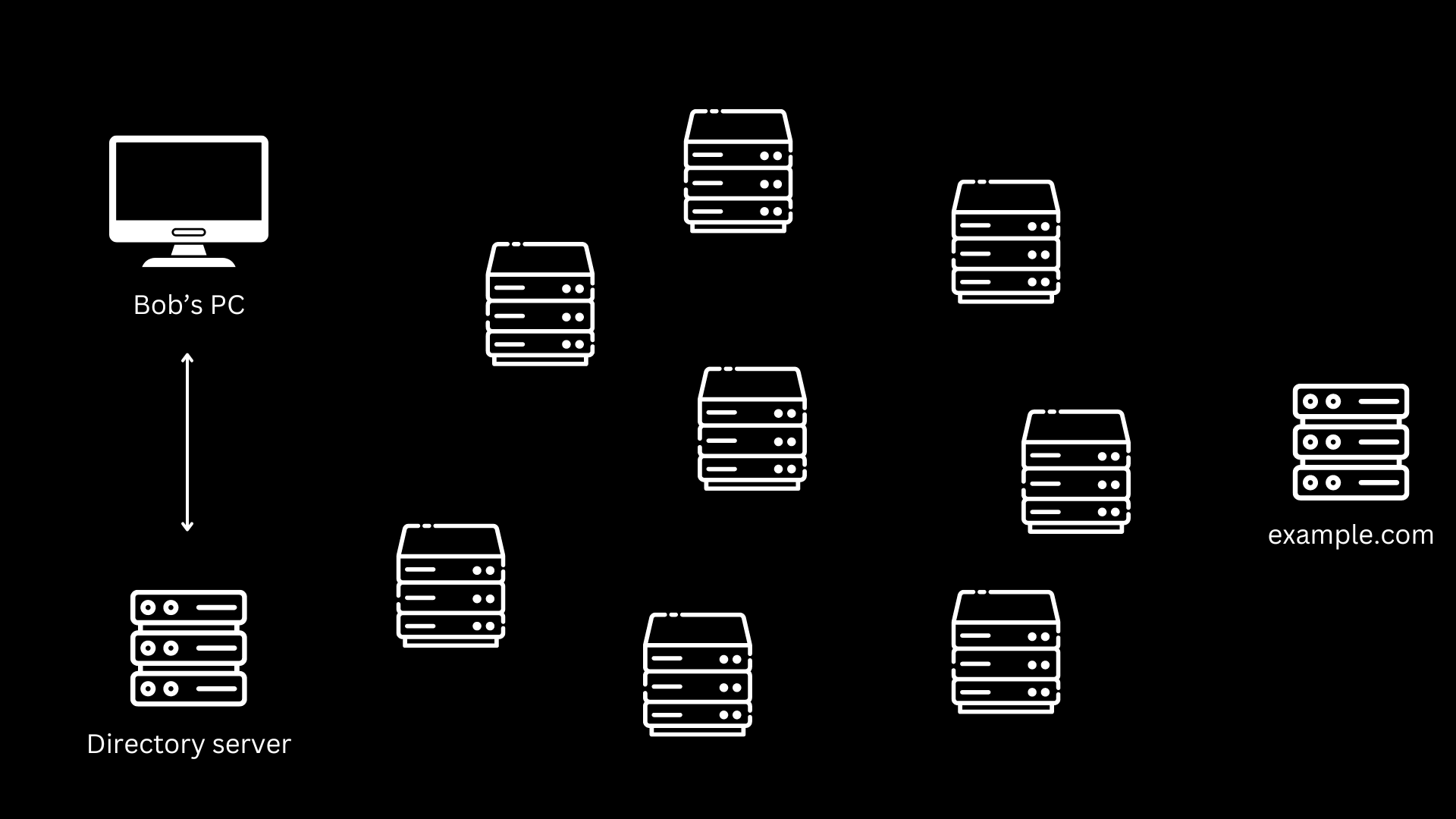
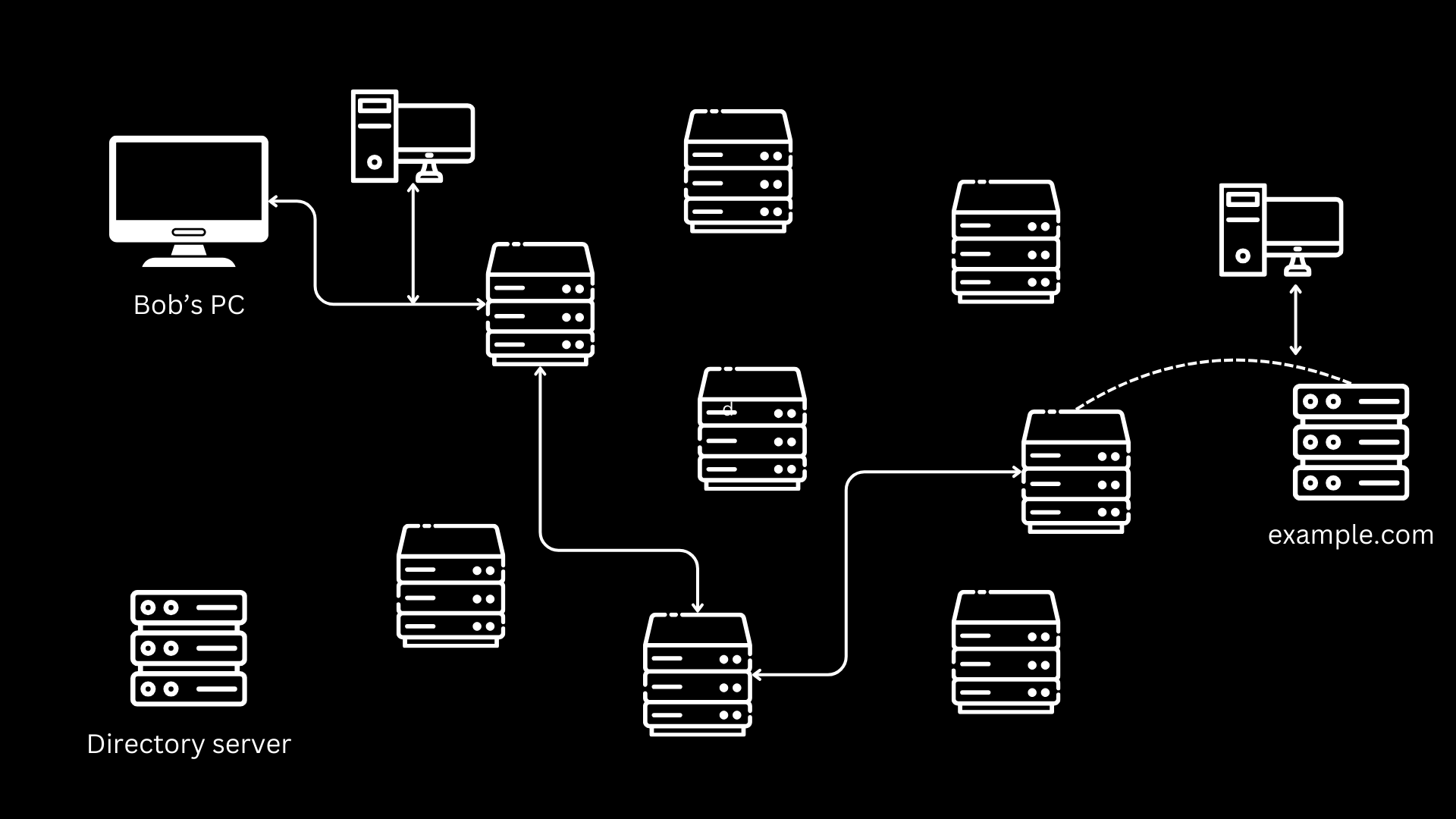
When a client or a user starts Tor, it grabs all the list of all the available relays from a directory server, the client then chooses a random path to the destination using the relay, each node only has the data about which node gave the data and which node it is sending the data next, these nodes can be anywhere in the world and no relay knows the entire network path the data is going through.
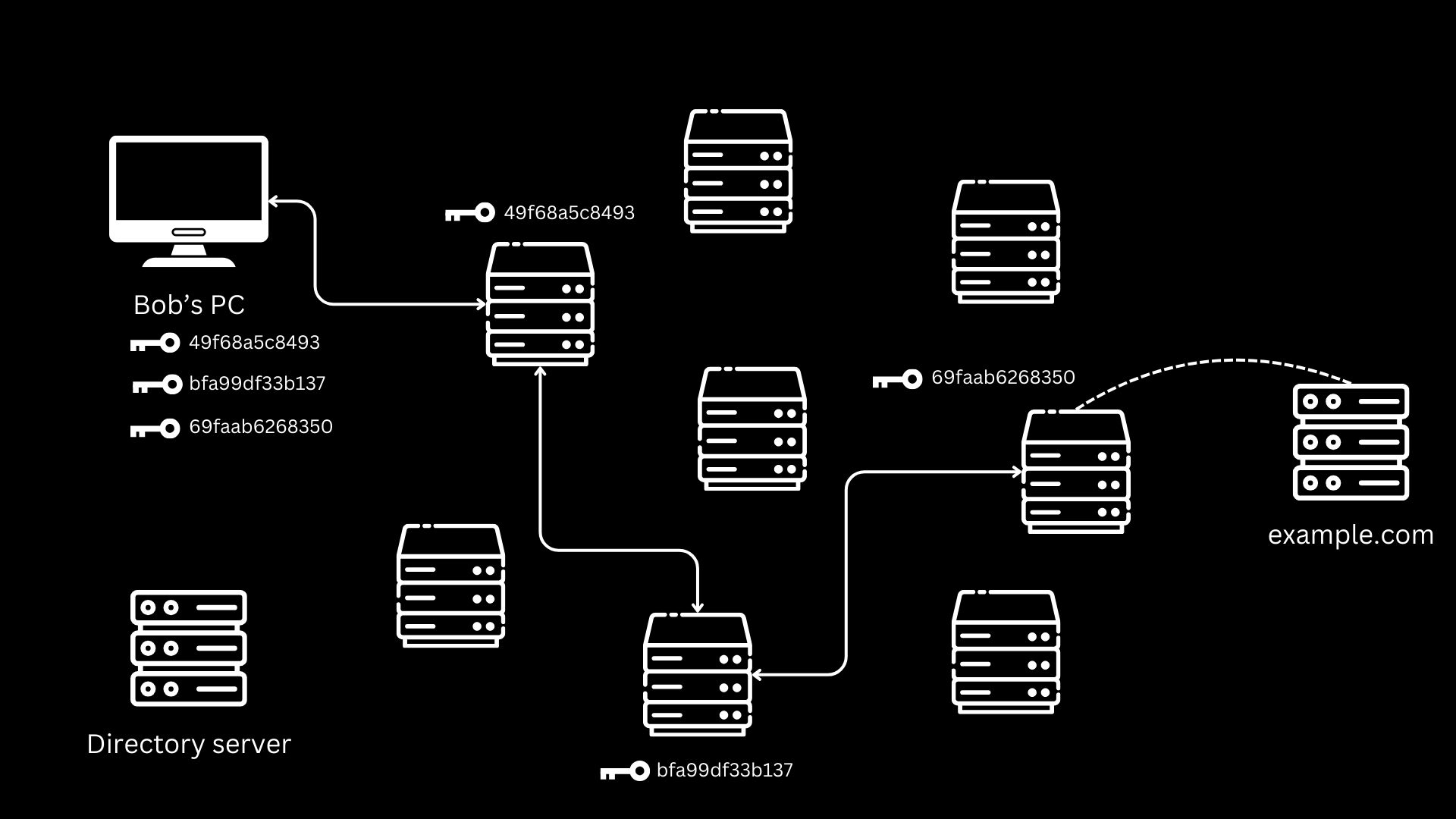
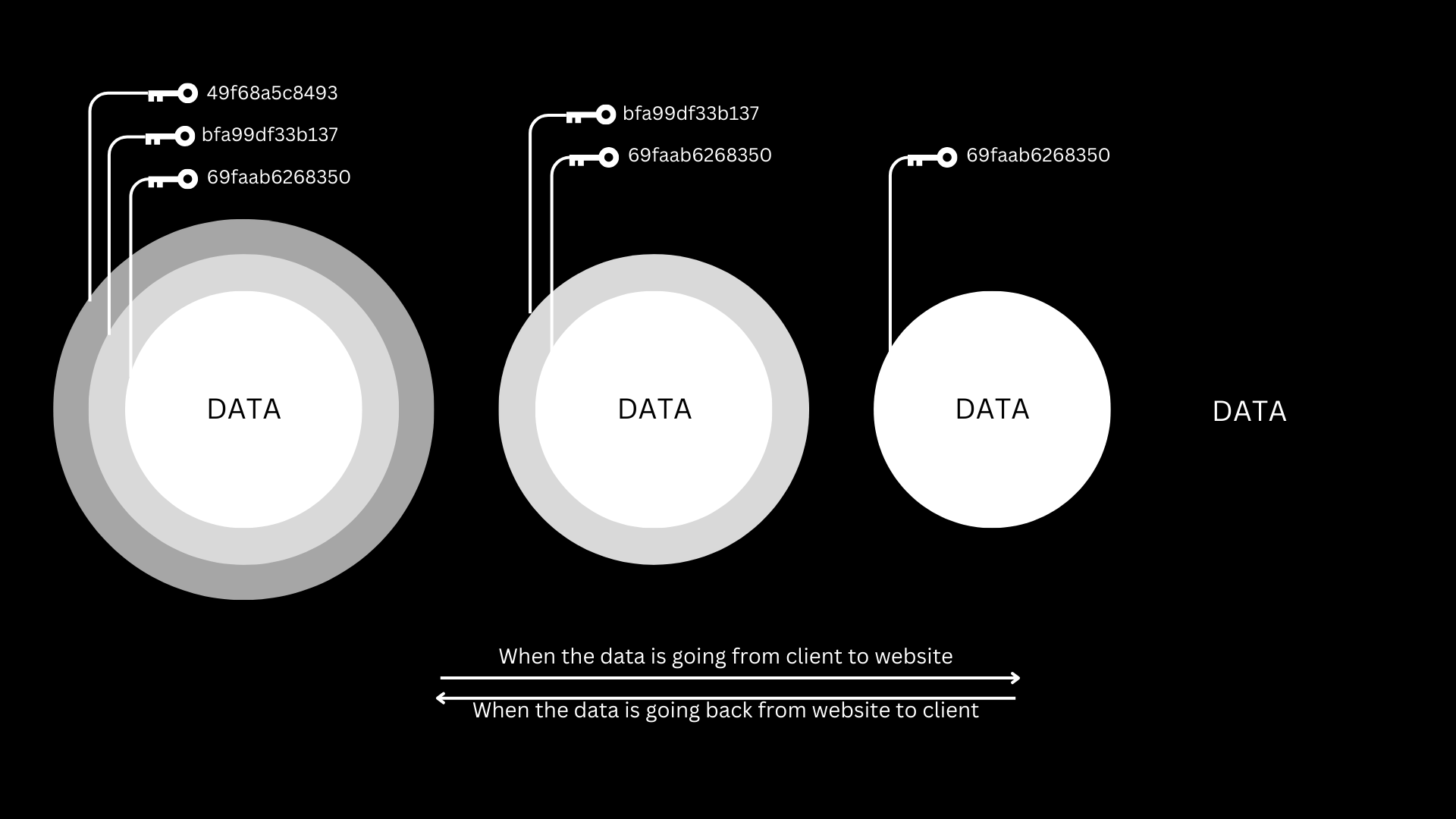
The client also generates a set of symmetric encryption keys for each node, to prevent logging and tracking of the request or the data as it passes through these nodes. The client encrypts the data with the keys and the sends it to the first node in the relay, the relay decrypts the data it revived with it's decryption key, which revels the information about the next node, the data is then passed on to the next node which again decrypts the data using it's key which again revels the information about the next node and the data is sent to that node, the node decrypts the last layer of encryption with it's key which reveals the data and the information about what to do with that data, for example the user wants to visit a page the data would contain information such as the website URL. This node then makes a request to the website and therefore exiting the Tor relay as it's not forwarding to another node making it the exit node. The website only knows the IP of the exit node as it's making the request and not the client. The website then sends the site data to this exit node which encrypts it with it's key and sends it to the intermediate node, which again encrypts it with it's key and sends it to the entry node, and you guessed it, the entry node encrypts the data one last time before sending it to the client. All these encryption layers are then decrypted as client has all the keys with it.
Why use Tor?
Although Tor sounds great for anonymization, an average user probably won't have the need to use Tor, unless you're doing some sketchy things online and want to hide from the government, you sure can use a VPN but there are chances that the VPN provider will log the user data which can be used to identify the user. Tor is also used by whistleblowers to leak information about an organization anonymously, but for an average user just surfing the web wouldn't have to hide from the government, and using Tor would just make the network speeds slower as the data through multiple nodes across the world before it reaches it's destination. And just like everything else Tor is not perfect, if a threat actor was able to monitor or sniff the packages at the entry node and the exit node of the network he can figure out the user and the data being sent by analyzing the network traffic.
Let's say Bob sent 50Mb of data and an attacker who's sniffing the network at the entry and exit node sees that 50Mb of data is being sent and 50Mb of data came out of the exit node, he can have a rough idea about Bob and can use various other methods to get more information about Bob.
The data coming out of the exit node is just a regular request, if a user does not use HTTPS can see and manipulate all the data that is being sent to the server, although Tor provides can anonymize user, it is point less once the user logs in, creates an account, or makes a transaction as all the activities you do on the site can be traced back to your account.
How to use tor?
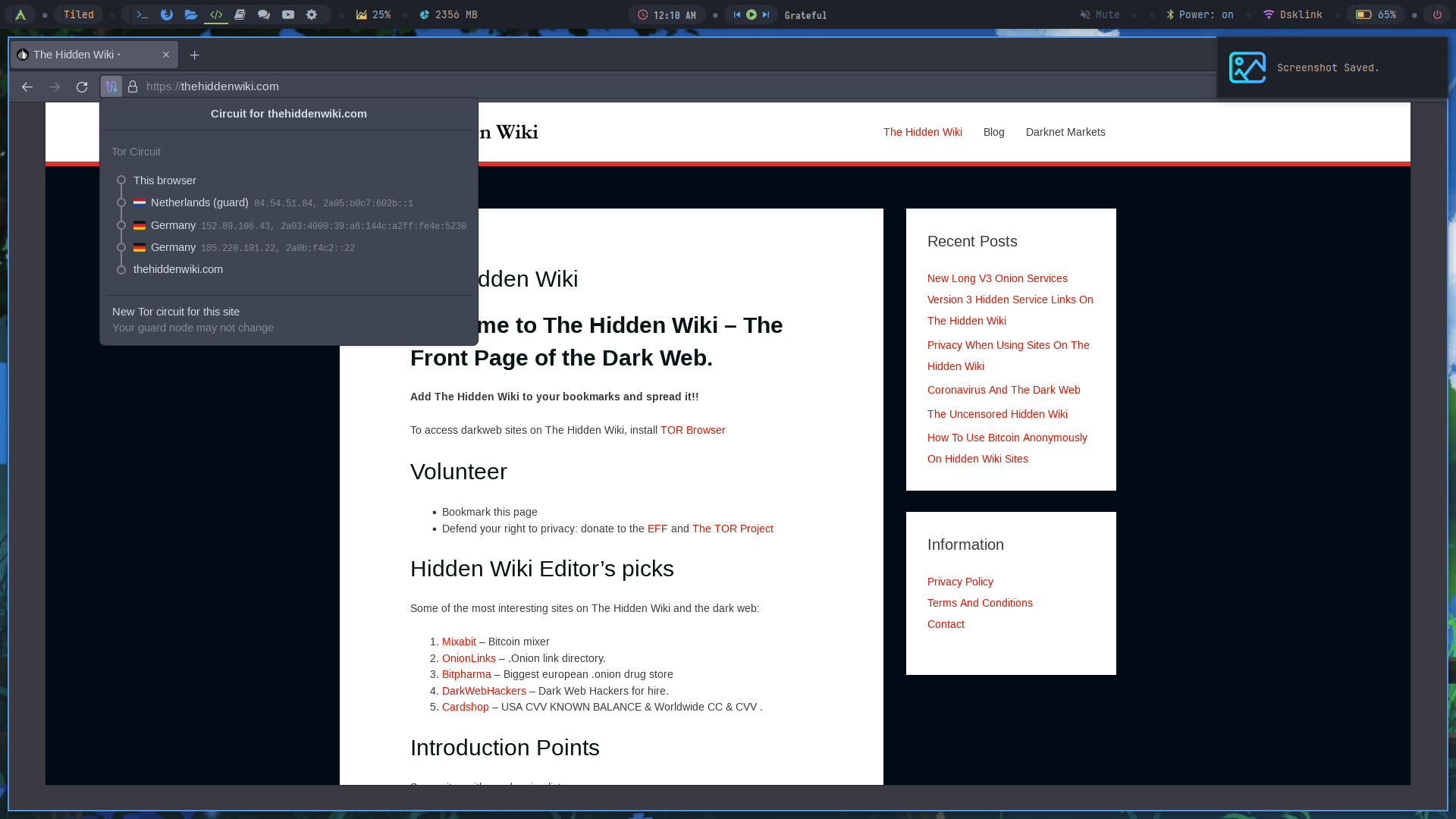
To use Tor we need to install the Tor browser, after installing the browser connect to the network and you're all good to go, just make sure to disable java script and change the browsing mode to "Safest" in the settings.
You can see your tor nodes by clicking on the tiny icon after the reload button.
Also Tor can be used to access Dark Web but we'll save it for another blog.
As we wrap up this journey through the layers of online anonymity, remember: TOR isn't just a browser, it's a shield against the tears of privacy breaches. So, let's navigate the web with the confidence that our secrets are as safe as a well-protected onion!